- File manager for Mac
- FTP port – how to forward and open access
FTP port – how to forward and open access
When talking about FTP lots of users do not understand a word, whereas others are familiar with this term. However, if to figure out what it is and how it is used you will definitely benefit from its features. In this article, we will highlight major aspects of FTP protocol, namely about FTP port, why you need it, and how to configure it. Along with it, you will get useful tips concerning changing the default FTP port or unlocking it in the firewall/router. Enjoy reading.
Defining the FTP port term
FTP ports are nothing more than communication endpoints. The main goals of which are to ensure connection and file transfer between your computer and server. When establishing a connection with a specific server, you should know its IP address. Even though the certain IP address is related to a certain server, the ports are the numbers used to identify the apps and the services you want to establish a connection with on a certain server.
If IP addresses are unique and there can be no two IP addresses for a certain server, when it comes to FTP port there is no certain number. The range of FTP port number can vary from 0 to 65535. So as you see, there is no clear answer to what port FTP use, as the number can be different.
However, to know how FTP ports work as well as how to configure them, you should first start with understanding the main features of FTP, FTP clients, and FTP servers. So let’s start from the very beginning.

List of FTP Features
The main purpose of the FTP protocol is to provide fast data transfer. However, the list of its features covers more than that. Below we have gathered the main features of the FTP protocol.
Representation of data
There are two main types of files used when transferring files using the FTP protocol: ASCII and binary. However, one can also use EBCDIC. ASCII files contain plain text. These files can be without extension or with a .txt extension. Binary files are programs and other non-text files saved in the format of the application that created them, or in the format of archived or compressed files. As for EBCDIC transfer type, well it is recommended for exchanging files between systems that support EBCDIC. This will avoid double conversion from ASCII to EBCDIC and vice versa.
File organization and Data structures
Both structured and nonstructured files can be transferred via FTP. Non-structured files are byte streams and are usually marked with EOF at the end. The structure record file is divided into records for text files and is marked with EDR at the end. The page structure file is divided into pages, each page has a page number and a page title. Random access or sequential access can be performed.
Transmission method
FTP transfer mode has 3 modes, namely streaming mode, block mode, and compressed mode.
Stream mode
Data is transmitted as a stream of bytes in the default settings of FTP. the data is divided into segments by TCP. There is no need to specify EOF while closing data. However, in case the file is divided into records EOR and EOF are required.
Block mode
The file is transferred as a block, and the block has its own 3-byte header. Main bytes include 16-bit values and 8-bit description subcodes.
Compressed mode
In the compressed mode, since the data is compressed, there are many advantages to increasing the throughput. While compressing text files blank spaces are removed. Whereas while compressing binary files, the null characters are removed.
Error control
There is no point in an extra mechanism of recovery after errors, as FTP uses TCP for data transfer.
Access control
There is a secure mechanism for accessing the system via password and the name of the user.
FTP operation
Based on a client-server architecture, by default, FTP uses 2 TCP connections for performing data transfer. One is a control connection the other is a data connection.
Control Connection
The control connection is established as a normal client-server connection. The server makes a passive open to a well-known FTP port (21) and waits for a connection request from the client. The client does an active open on TCP port 21 to establish a control connection. The control connection exists as long as the client communicates with the server. This connection is used to send commands from the client to the server and to send responses from the server. The IP service type for the control connection is set to get the “lowest latency” since commands are usually entered by the user.
Data Connection
Opens every time a file is transferred between the client and the server and closes every time after the data has been sent. Transfer data can occur between the data transfer processes of a DTP server and a DTP and a client, or between a DTPS of two servers. FTP port (20) is used. The IP service type of the data connection should be “maximum bandwidth” because that connection is used for file transfers.
What is an active and passive mode? How are they associated with ports
The fact is that there are two options for the development of a client-server interaction scenario. Depending on the method of establishing a connection for data transfer, active and passive FTP operation modes are distinguished. In the active mode, the server itself establishes a data transfer connection to the client, in passive, vice versa. Let’s consider these modes in more detail.

The fact is that in the FTP protocol there are two types of connection:
- Control connection.
- Connection for data transfer.
The activity and passivity of the client appear only in the second type of connection. Whereas the first is necessary so that the server and client can communicate with each other. That is so that the server receives commands from the client because this connection is called the control. Such a connection works through a standard FTP port installed by default or in other words the default FTP port.
The main difference between the active and passive modes of the FTP protocol is which of the client-server bundles makes the connection for data transfer, that is, roughly speaking, who is connected to whom. The ports to which data is transmitted also differ.
With the active mode of operation, the client makes a control connection to the server, but the server itself makes the connection for data transfer.
In a passive mode of operation, the data connection, as well as the control connection to the server, is initiated only by the client. That is, in active mode, the server connects to the client for data transfer, and in passive mode, the client connects to the server.
How to establish FTP Active Mode
Both in the active and in the passive mode, the connection starts with sending a request by the client to the server. First, a control connection is established. To do this, a temporary port is created on the client with a number in the range from 1024 to 65535 for establishing a control connection, as well as a port for data transfer. In the active mode, everything happens in the following order:
1. The client sends a request to the server port number 21 (default port for FTP) from the temporary port in the range 1024–65535.
2. The server responds to a temporary client port.
3. The client confirms the connection.
4. The client sends an FTP PORT command that talks about using the active FTP mode, its IP address, and also the port number for establishing a data connection to which the server will connect.
5. The command is confirmed by the server.
6. The client instructs the server to work with FTP.
7. The server creates a data connection. To do this, it sends a request from port 20 to the port specified by the client in the fourth paragraph.
8. The client responds to the request.
9. The server confirms the connection and allows the client to transfer data.
How to establish FTP Passive Mode
In passive mode, the procedure for establishing a data connection is slightly different. Actions occur as follows:
1. The client sends a request to the server port number 21 (FTP default port) from the temporary port in the range 1024–65535.
2. The server responds to a temporary client port.
3. The client confirms the connection.
4. The client sends a PASV command that talks about using passive FTP mode.
5. The server confirms the work in passive mode, sends its IP address, as well as the port number for establishing a data connection to which the client will connect.
6. From the port for data transfer, the client sends a request to establish a connection to the port issued by the server.
7. The server confirms the connection.
8. The client establishes a connection.
9. The client instructs the server (from the control port to FTP port 21), after which data can be transmitted.
Solving problems with Firewall
In the active mode, the main problem occurs with the client. If the Firewall is configured to drop incoming connections not initiated internally, the server will not be able to establish a data connection. And since the FTP data port is dynamic, there are some difficulties with configuring the Firewall. It will be most correct to specify the range of used ports in the client and create an allowable Firewall rule for them.
In passive mode, the server may encounter such a problem. The solution is similar: we specify the passive FTP port range used in the server settings and create an allow rule for it.
Why does FTP have 2 port numbers? Is it necessary to use 21 port?
User question:
I have a need where data needs to be FTP from my NAS to another machine outside my LAN. I've seen some YouTube videos but that has left me a bit confused so thought to ask the question here. What is the difference between opening a port (21) through the firewall versus setting up port forwarding for my needs?— from Reddit
People who constantly deal with servers and create them have heard about the number 21. For them, it is significant, as many servers and protocols, not only FTP, use 21 port. However, by default, FTP uses two specified ports, namely 20 and 21. Port 21 is mostly used for management whereas port 20 is for data transfer. It leads to the fact that port 21 is of greatest importance, which is necessary for you to open the server and send commands to it and port 20 is needed mainly for active mode.
21 – port is used to control data transfer. The client establishes (actively) a control connection to server port 21 (it opens the connection passively) to send FTP commands to the server and receive FTP responses from it. A control connection exists all the time while the client is communicating with the server. 21 port is the server port.
On the 20th port (server), in fact, data is transferred under the “supervision” of the control connection on port 21 (server). This 20-port is required for a connection that exists only at the data transfer. This distinguishes the specified connection from that on port 21, which exists all the time when the customer works with the server. 20 port is the server port.
Let’s return to port 21 and the ubiquity of its use. If you start to analyze the situation it is not shiny. After all, the data transfer protocol is not at all protected from interception. At any time, experienced hackers can attack your server and intercept the password and login of the client. Then they will infiltrate the server and steal important data from there, or they will hide malicious programs and viruses in directories.
In order to somehow increase the security level of using the FTP protocol, it is recommended to change the standard FTP port in the settings, this is needed for connection. It is not difficult to do this, but each server has this option configured in its own way. The only nuance is that when connecting, the client will need to specify a new FTP data port number instead of the number 21. This is the essence of protection – hackers will not know the port on which to intercept data, therefore they will not be able to steal it.
What are the common FTP vulnerabilities
The most significant drawback of the protocol is the transfer of all information, as well as usernames and passwords, in an open form. This makes it impossible to use this protocol to transfer confidential information without using third-party software and hardware. If the attacker has access to the communication channel through which this data is being passed, encryption must be used or secure FTP port number. This is a typical case of the passive impact of an attack – the server’s state does not change, the security policy is not violated, but there is access to the necessary information.
The protocol does not define actions that counteract the selection of passwords. After an incorrect password, the client is given the opportunity to re-enter it, but the connection is not disconnected. There are also no restrictions on the number of repetitions. As a result, an attack aimed at guessing passwords can last as long as you like, and the absence of delays in server responses increases efficiency.
The following vulnerabilities are associated with the passive mode of the protocol and the possibility of participation in the connection of the third node. When using the passive data transfer mode, in which the server tells the client which FTP server port to connect to in order to start the transfer, it is possible to establish a connection from another computer.
If the real client has already selected the file necessary for downloading and has the necessary access, then theft on his behalf is possible. An attacker, knowing the peculiarities of the choice of FTP port numbers by the FTP server for organizing passive mode, increases the likelihood of an attack success. To do this, you must try to establish connections with the ports, and if everything is successful, the file will be stolen. In the same way, you can write a file to the server on behalf of the registered user by establishing a connection with the FTP server port waiting for the file to start.
Let’s return to port 21 and the ubiquity of its use. If you start to analyze the situation it is not shiny. After all, the data transfer protocol is not at all protected from interception. At any time, experienced hackers can attack your server and intercept the password and login of the client. Then they will infiltrate the server and steal important data from there, or they will hide malicious programs and viruses in directories.
In order to somehow increase the security level of using the FTP protocol, it is recommended to change the standard FTP port in the settings, this is needed for connection. It is not difficult to do this, but each server has this option configured in its own way. The only nuance is that when connecting, the client will need to specify a new FTP data port number instead of the number 21. This is the essence of protection – hackers will not know the port on which to intercept data, therefore they will not be able to steal it.
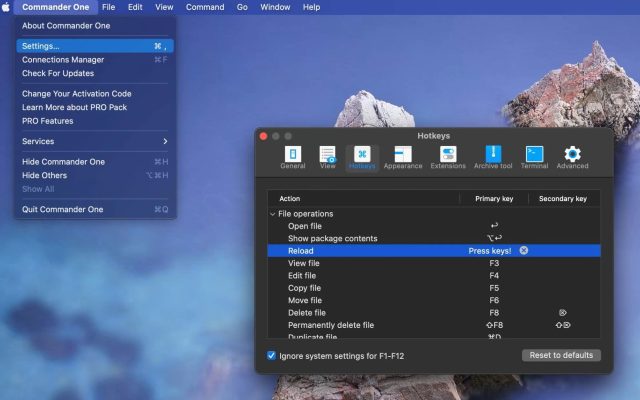
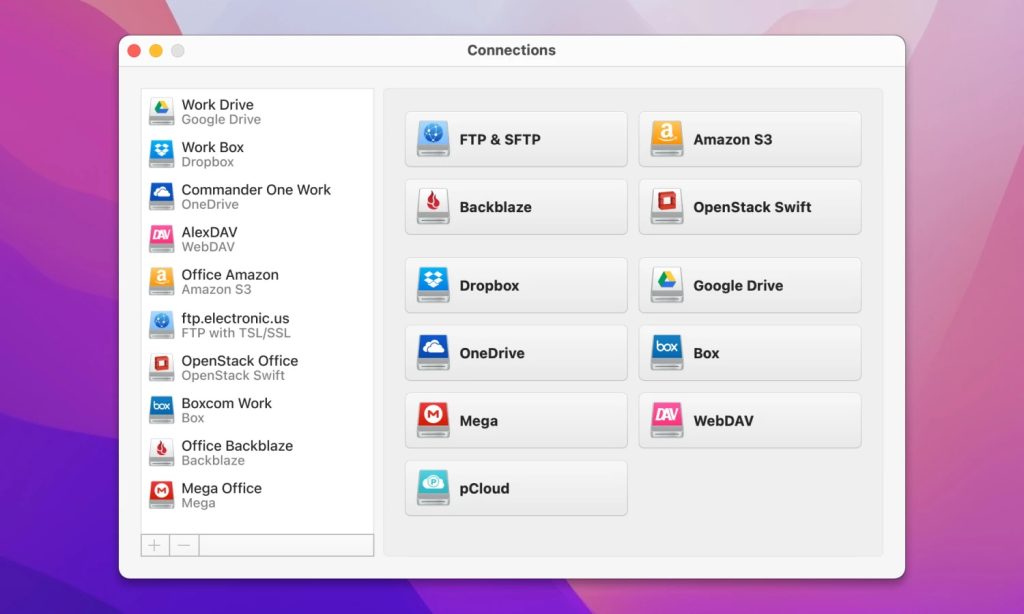
FTP Vulnerability Counteraction
Vulnerabilities of the protocol occur mainly due to its features and the lack of ways to protect the transmitted information. To increase security, you must use third-party tools, as well as carefully consider the interaction of network nodes via the FTP protocol. The problem of transferring all information in an open form is solved either by using encryption tools, where possible, or by protecting communication channels from unauthorized access. For example, Commander One, the app is a popular alternative to Cyberduck FTP client with the support for FTP/SFTP connections and cloud storages.
With this app you will not bother anymore whether FTP port secure is or not and simply rely on the encryption feature of the app, as it uses AES with a 256-bit key length. Besides that, the app supports a wide range of advanced features that are necessary when handling files, try this app to benefit from its functionality. Other problems can be solved by filtering.
To protect passwords from busting, you must configure the FTP server so that connections are closed after a number of password attempts. It is also necessary to provide a pause before responding to each incorrect password, which will significantly slow down their enumeration.
To prevent file theft during passive mode, filtering by IP address is required. While using this filtering, it becomes impossible to exchange between two servers initiated by the client, since the server, which is switched to active mode, will have an address different from the client’s address, and packets from it will be filtered. From the point of view of modern security, the correct solution is to use one of the encrypted FTP implementations (FTPS, SFTP) or use FTP through VPN.
SFTP port. The difference from FTP port
SFTP is a standard for transferring information on the Internet, which is designed to move and copy files using a connection of increased reliability and security SSH (Secure Shell). This type of connection can provide access and secure transmission, which is encrypted with both login and password, as well as the contents of the transmission, thereby protecting passwords and confidential information from open transmission on the network. Unlike FTP, the SFTP protocol, despite its similar functions, uses a different data transfer protocol, and therefore standard clients cannot communicate with SFTP servers.
While TCP port 22 is the general correct answer and is considered the default Mac SFTP port number, it depends on how SSH is configured to use a SFTP standard port rather than an alternative port.
Since SFTP acts as an SSH subsystem, it runs on any port that listens for the SSH daemon and is configured by the administrator. SFTP typically uses SFTP port number 22, but can be configured to work on almost any port. SFTP is just one of the protocols that can be launched via SSH (others include a virtual terminal). In fact, SFTP is independent and can work even without using SSH.
Key differences between FTP and SFTP
- FTP does not provide any secure channel for transferring files between hosts, while SFTP provides a secure channel for transferring files between hosts on a network.
- FTP is short for File Transfer Protocol, while SFTP is short for Secure File Transfer Protocol.
- FTP is a service provided by TCP/IP. However, SFTP is part of the SSH protocol, which represents information for remote login.
- FTP establishes a connection using a control connection on TCP port 21. On the other hand, SFTP transfers the file over a secure connection established via SSH between the client and the server.
- FTP transfers the password and data in text format, while SFTP encrypts the data before sending it to another host.
FTP Port: Frequently Asked Questions
FTPS ports are just TCP ports that are reserved for secure or encrypted file transfer. By default, these are ports 989 and 990, so you probably shouldn’t use these for other things.
It is possible to use a browser, for this purpose it is necessary to type in the address bar of the browser ftp: // your_login: your_password @ domain_name of your site. However, keep in mind that the browser is not FTP enabled. Technically, it can do this, but many of the necessary functions are missing in it.
The disadvantage of this method is the following: to work in active mode, the client requires a specified IP address. Also, certain difficulties will arise when finding a client behind a firewall or NAT.
By default, 20 and 21 ports are configured in FTP. The most important is the 21 port, as it is needed to open the server and send commands to it(so-called control connection). Whereas port 20 is needed mainly for active mode.
FTP uses TCP in communication. TCP is the basic transport protocol of the Internet, which provides data delivery over a connection pre-established between two computers. The connection works throughout the communication session.
The UDP protocol is designed to quickly transfer a portion of data without a delivery guarantee and without pre-establishing a connection.
The developers thought that the amount of data transmitted through the data port would make it impossible to send control commands in a timely manner, so they used two ports – the control connection is initiated by the client and the data channel by the server.